Java, Python, Ruby, C++, etc. One must familiar with different ways to structure design, implement and test the project based on the programming language.HTML5, CSS3, BootStrap, AngularJS, VueJS, ReactJS, JavaScript, Angular, etc. The understanding of third-party libraries like jQuery, Ajax, SASS, adds more advantages.Spring, Spring Boot, MyBatis, Django, PHP, Hibernate, js, yin, and more.MySQL, Oracle, SQLite, Postgres, MongoDB, Cassandra, Apache storm, Sphinx, etc,.UI and UX design is also necessary.Apache or NGINX would be beneficial. Good knowledge of Linux helps enormously when administering servers.
// ES5 Function Constructor
function Person(name) {
this.name = name;
}
// ES6 Class
class Person {
constructor(name) {
this.name = name;
}
}Student class that subclasses Person and add a studentId field, this is what we have to do in addition to the above.// ES5 Function Constructor
function Student(name, studentId) {
// Call constructor of superclass to initialize superclass-derived members.
Person.call(this, name);
// Initialize subclass's own members.
this.studentId = studentId;
}
Student.prototype = Object.create(Person.prototype);
Student.prototype.constructor = Student;
// ES6 Class
class Student extends Person {
constructor(name, studentId) {
super(name);
this.studentId = studentId;
}
}| S.N. | Basis of Comparison | Get | Post |
|---|---|---|---|
| 1 | Purpose | The Get request is designed for getting data from the server. | The Post request is designed for sending the data to the server. |
| 2 | Post Mechanism | The request is sent via URL. | The request is sent via an HTTP request body. |
| 3 | Parameter Passing | The request parameters are transmitted as a query string appended to the request. | The request parameters are transmitted with the body of the request. |
| 4 | Default | It is the default method hence it implements automatically. | We need to specify manually. |
| 5 | Capacity | We can send limited data with the Get request. | We can send a large amount of data with the Post request. |
| 6 | Data Type | It always submits data as text. | We can send any type of data. |
| 7 | Security | The use of Get is safe because it is idempotent. | The use of Post unsafe because it is non-idempotent. |
| 8 | Visibility of Data | The data is visible to the user as it puts the data in the URL. | The data is not visible to the user as it puts the data in the message body. |
| 9 | Bookmark and Caching | The Get request can be bookmarked and caching. | The post request cannot be bookmarked and caching. |
| 10 | Efficiency | It is more efficient than post. | It is less efficient. |
| 11 | Example | Search is the best example of Get request. | Login is the best example of a Post request. |
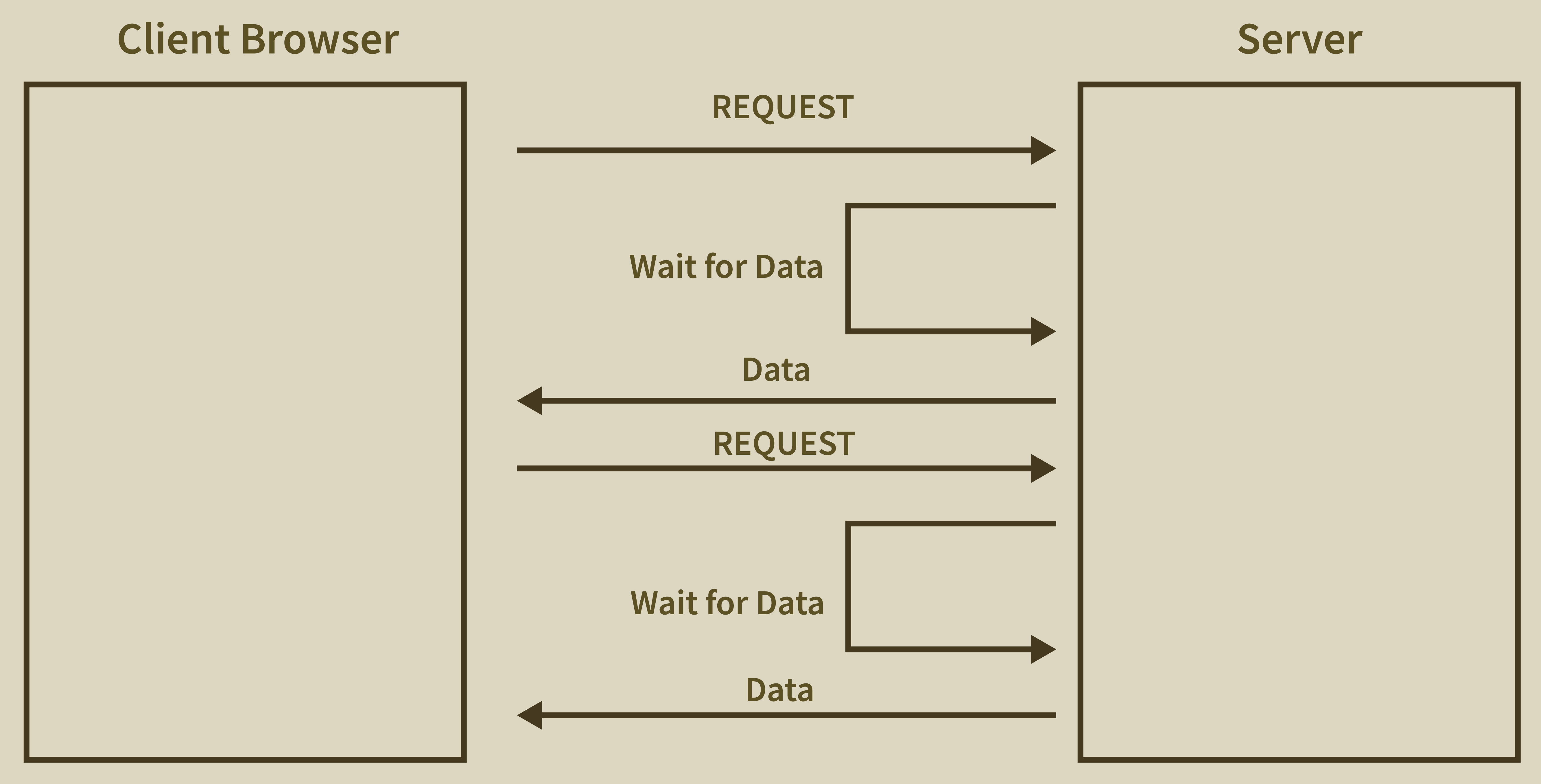
Node.js is a single-threaded application but it supports concurrency via the concept of event and callbacks. As every API of Node js is asynchronous and a single thread, it uses async function calls to maintain the concurrency. Node uses an observer pattern. Node thread keeps an event loop and whenever any task gets completed, it fires the corresponding event which signals the event listener function to get executed. -> extra code in your client.=> extra work before you get results.=> new libraries that you don’t know yet.count1 = (fun(x) + y) * (fun(x) - z);
temp = fun(a);
count2 = temp + y * temp - z; count1 and count2 will be equal if the value of fun(x) is not reflected. If the variable count1 is not equal to the variable count2, the referential transparency is violated.| Normalization | Denormalization |
|---|---|
| Normalization involves removing redundant data (multiple copies of data) from a database and storing consistent, non-redundant data. | It involves combining data from multiple tables into a single so that it can be queried quickly. |
| It primarily focuses on clearing out unused data and reducing duplicate data and inconsistencies from a database. | On the other hand, denormalization aims to achieve faster query execution by adding data redundancy. |
| During normalization, tables are reduced in number due to the reduction of data in the database. | Denormalization, on the other hand, involves integrating data into the same database and therefore the number of tables to store the data increases. |
| Data integrity is maintained by normalization. A change to the data in the table will not impact its relationship with the other table. | Data integrity is not maintained by denormalization. |
| It optimizes the use of disk space. | It does not optimize disk space. |
onFulfilled() method, a promise will be in fulfilled state.onRejceted() method, a promise will be in rejected state.| Abstract | Interface |
|---|---|
| An abstract class can have abstract and non-abstract methods | The interface can have only abstract methods. |
| An abstract class can have static, non-static, final, non-final variables. | The interface has only static and final variables. |
| An abstract class can provide the implementation of the interface. | Interface can’t provide the implementation of an abstract class. |
| An abstract class can be extended using the keyword "extends". | An interface can be implemented using the keyword "implements". |
| A Java abstract class can have class members like private, protected, etc. | Members of a Java interface are public by default. |
{ } " surrounding them. On the other hand, var doesn't have such a restriction. console.log(varNumber); // undefined
console.log(letNumber); // Throws the reference error letNumber is not defined
var varNumber = 3;
let letNumber = 4;function timesTwo(params) {
return params * 2
}
timesTwo(5); // 10var timesTwo = params => params * 2
timesTwo(5); // 10var var1
var var2 = null //assigning null value to the variable var2
console.log(`var1 : ${var1}, type : ${typeof(var1)}`)
console.log(`var2 : ${var2}, type : ${typeof(var2)}`) Var1 : undefined, type : undefined
var2 : null, type : object var1 is undefined also its type is undefined. Because we have not assigned any value to the variable var1. The value null is assigned to the variable var2. It prints its type as abject. Since null is an assignment value and we can assign it to a variable. Therefore, JavaScript treats null and undefined relatively equally because both represent an empty value.| GraphQL | REST |
|---|---|
| GraphQL is an API design architecture, but with a different approach that is much flexible. | REST is a robust methodology and API design architecture used to implement web services. |
| It follows client-driven architecture. | It follows server-driven architecture. |
| It does not deal with the dedicated resources. | It deals with the dedicated resources. |
| It has a single endpoint that takes dynamic parameters. | It has multiple endpoints. |
| It provides stateless servers and structured access to resources. | It provides stateless servers and flexible controlled access to resources. |
| It is elastic in nature. | It is not rigid in nature. |
| It supports only JSON format. | It supports XML, JSON, HTML, YAML, and other formats also. |
| The client defines response data that it needs via a query language. | Data represented as resources over HTTP through URI. |
| It provides synchronous and asynchronous communication in multiple protocols such as HTTP, MQTT, AMQP. | It provides synchronous communication through HTTP only. |
| Its design based on HTTP (status, methods, and URI). | Its design based on message exchange. |
| It provides high consistency across all platforms. | It is difficult to achieve high consistency across all platforms. |
| Development speed is fast. | Development speed is slow. |
| Resetting | Normalizing |
|---|---|
| Removes all the built-in browser styling. | Normalizing makes elements render consistently across browsers. |
| Provides bug fixes | Includes bug fixes |
Java, C#, or C++ you start by creating a class–a blueprint for your objects – and then you can create new objects from that class or you can extend the class, defining a new class that augments the original class.new, JavaScript injects an implicit reference to the new object being created in the form of this keyword. It also returns this reference completely at the end of the function.function Foo() {
this.kind = ‘foo’
}
var foo = new Foo();
foo.kind //=> ‘foo’clear CSS property specifies whether an element can be next to floating elements that precede it or must be moved down (cleared) below them.| Basis of Comparison | Fail Fast Iterator | Fail Safe Iterator |
|---|---|---|
| Operates | It operates directly on the collection itself. | It operates on a cloned copy of the collection. |
| Exception | It throws a ConcurrentModificationException in modifying the object during the iteration process. | It does not throw Exception. |
| Clone Object | No clone object is created during the iteration process. | A copy or clone object is created during the iteration process. |
| Memory utilization | It requires low memory during the process. | It requires more memory during the process. |
| Modification | It does not allow modification during iteration. | It allows modification during the iteration process. |
| Performance | It is fast. | It is slightly slower than Fail Fast. |
| Examples | HashMap, ArrayList, Vector, HashSet, etc. | CopyOnWriteArrayList, ConcurrentHashMap, etc. |
| ServletContext | ServletConfig |
|---|---|
| ServletContext represents the whole web application running on a particular JVM and common for all the servlet. | ServletConfig object represents single servlet. |
| It is just like a global parameter associated with the whole application. | It is the same as the local parameter associated with a particular servlet. |
| It has application-wide scope so define outside servlet tag in the web.xml file. | It is a name-value pair defined inside the servlet section of web.xml files so it has servlet wide scope. |
getServletContext() method is used to get the context object. |
getServletConfig() method is used to get the config object. |
| To get the MIME type of a file or application session related information is stored using a servlet context object. | The shopping cart of a user is a specific to particular user so here we can use servlet config. |
Thread.join() Method : We can get a deadlock if two threads are waiting for each other to finish indefinitely using thread join. If a thread has to wait for another thread to finish, it's always best to use join with the maximum time you want to wait for the thread to finish.| Constructor Injection | Setter Injection |
|---|---|
| There is no partial injection of dependencies. | There can be a partial injection of dependencies. |
| It does not override the setter injection value. | It overrides the constructor injection value if both are defined. |
| It always creates a new instance if any modification occurs. | It does not create a new instance if we made any changes to it. |
| Using constructor injection is better for too many properties. | Using setter injection is better for few properties. |
| It makes bean class objects as immutable. | It makes bean class objects as mutable. |
import java.util.*;
public class Demo
{
public static void main(String args[])
{
-------------------
-------------------
Map<String, Map<String, Integer>> map = new HashMap <String, Map<String, Integer>> {{
put ("VEGETABLES", new HashMap<String, Integer>() {{
put("Tomato", 300);
put("Onion", 50);
put("Carrot", 100);
put("Beetroot", 40);
}}
--------------------
-------------------
);
}};
System.out.println(map);
}
}